How Long Does It Take To Crack Your Password?
Key Points
- Brute force attacks using algorithms are often used to compromise a password.
- When a person creates a password, it is hashed and compared to the value stored in the system. If the two hashes are identical, the login is successful.
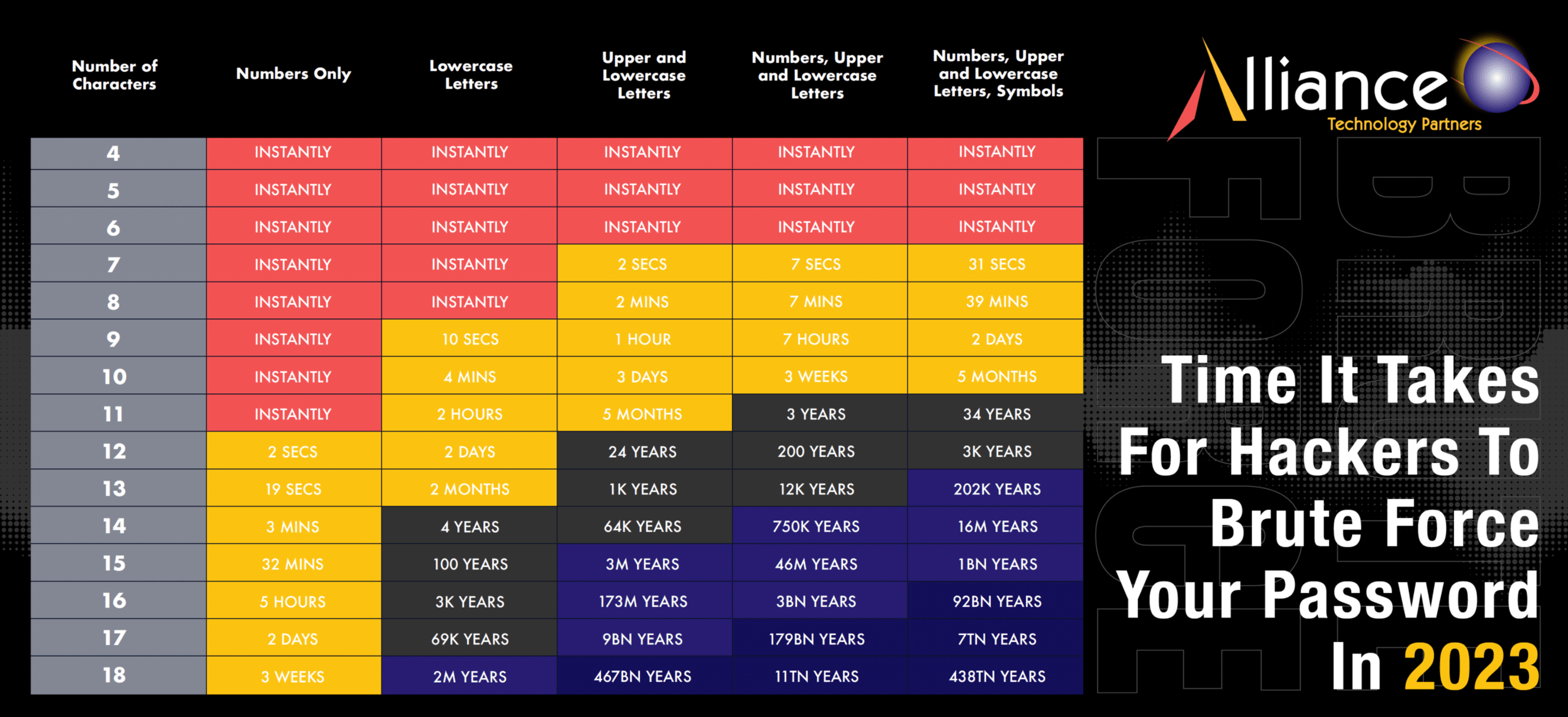
- A password that is 18 characters in length and contains a combination of numbers, lowercase letters, uppercase letters, and symbols could take up to a staggering 438 trillion years for the average hacker to crack.
- To avoid your passwords being compromised, you must use a combination of letters, numbers, and symbols, regularly update them and use two-factor authentication.
How can a password be compromised? Are there specific techniques or methods that are commonly used to gain access? What are the key factors determining whether a password is secure? What distinguishes a strong password from a weak one?
These questions about password security are all great ones. Many people focus on the technical details of creating a strong password but don’t always explain the reasoning behind it. The truth is that password security is a complex topic with many nuances. Trying to determine someone’s password by guessing based on personal knowledge is simple. Still, it is not always successful, mainly due to the maximum login attempts policies implemented by most applications and websites.
One would need a general idea of the password to guess a password successfully. Otherwise, the risk of being locked out is high. Another way to compromise a password is using algorithms, commonly known as brute force attacks. Understanding the basics of cryptography is necessary to comprehend the security of passwords. Cryptography can be divided into three categories: a private key, a public key, and hash functions.
Download our cheat sheet on how long a hacker can take to crack your password here.
The Role of Hashing in Password Security
Hashing is a method of converting a given string into a fixed-length output. When a person creates a password, it is hashed and compared to the value stored in the system. If the two hashes are identical, the login is successful. This operation is a brute-force attack and is the basis of many password-cracking tools. The strength of a password depends on its ability to resist a brute-force attack.
The only method to decrypt a hash is by attempting every possible input until the original hash is matched. The Secure Hash Algorithm (SHA-256) is a widely used industry standard for hashing. SHA-256 generates a complex string of characters upon inputting even a simple password, like “password”. Even the slightest alteration to the original string – such as capitalizing a letter (e.g., “Password”) – will completely change the outputted hash.
Hashed passwords are irreversible due to their one-way encryption algorithms. However, hackers can generate lists of possible character combinations to replicate the encryption process. Then, they can search through these lists and compare them with the hashed passwords stored in the system, allowing them to determine the original passwords.
It is no easy feat, but it can be accomplished by an experienced hacker armed with only basic tools. The complexity of the process requires a great deal of expertise and technical know-how, but the potential for success is there. With the right resources and guidance, a hacker has the potential to infiltrate and exploit any vulnerable systems.
Cracking a hash requires tremendous computing power, so other methods are typically used to compromise passwords. This is why it is essential to take extra care when constructing and protecting passwords, as a breach in security can lead to devastating consequences.
Treat Your Passwords Like Your Underwear
The old saying “treat your passwords like your underwear” holds true regarding password security. Passwords and underwear are similar in that they are personal and private and should be kept that way. Here are some ways that passwords are like underwear:
- Like you should change your underpants regularly, you should change your passwords regularly to prevent unauthorized access.
- Passwords, like underwear, are not meant to be shared with others. Only authorized individuals should have access to your passwords.
- You shouldn’t leave your passwords where others can find them, just like you wouldn’t leave your underwear out in the open.
You should try to create passwords that are not easy to guess, as they will be more secure. Additionally, using two-factor authentication can help ensure that your account will still be denied even if a password is cracked.
How Long Does It Take To Crack a Password?
The amount of time it takes to crack a password largely depends on the strength of the algorithm used to hash it. A password with eight characters comprising numbers, upper-case letters, lower-case letters, and symbols can be cracked in under an hour. A shorter or less complex password can be hacked instantly, or in minutes, by any hacker with basic knowledge and equipment.
Meanwhile, a password that is 18 characters in length and contains a combination of numbers, lowercase letters, uppercase letters, and symbols could take up to a staggering 438 trillion years for the average hacker to crack. Such complexity renders it virtually impossible for hackers to gain access, providing the user greater security. The importance of using strong, secure passwords cannot be overstated – it is the first line of defense in protecting your information from unauthorized access.
Keeping this in mind, it is vital to take the necessary steps to ensure that your passwords are as strong and secure as possible. A good rule of thumb is using a different password for every account, avoiding common words and phrases, and keeping your passwords well-protected.
Creating a Strong Password Can Be Your Ticket to Online Safety
Understandably, no one wishes to remember lengthy and complex passwords, especially an 18-character one. While the former might be difficult to recall, it is nothing compared to the time a hacker could take to decipher it – which may range from trillions of years. However, with 11 characters – which should incorporate a mixture of numbers, uppercase and lowercase letters, and symbols – it could take a hacker up to 34 years to crack, which is significantly more secure than a password of just eight characters.
It is also important to remember that passwords should be regularly updated and stored securely. By following these precautions and using two-factor authentication where possible, you can help to protect your accounts from unauthorized access. Creating a strong password may seem like a lot of work, but it is worth your time and effort to ensure that your data remains secure. By taking the necessary steps, you can rest assured that your online accounts are safe and secure. After all, the only person who should have access to your passwords is you.
Final Thoughts
There is no excuse for not taking security seriously in the digital age. Despite the potential consequences, too many people use short, generic, and weak passwords that are easily guessable for automated software. This negligence risks their own data and leaves them vulnerable to cybercriminals. Lack of attention to password security can lead to severe consequences, including identity theft, financial loss, and personal and professional reputation damage. Creating strong, unique passwords and updating them regularly is essential to keep your online accounts secure. It’s also important to be mindful of the security practices of your websites and online services and be wary of suspicious emails and messages. Take the necessary steps to protect yourself and your personal information from cybercriminals today.


