
Not All Managed IT Services Providers Are The Same
Not All Managed IT Services Providers Are The Same: Unveiling Our Top 10 Differentiators In an ever-evolving digital landscape, businesses need managed IT services to[...]
FBI Issues Cybersecurity Threat Warning
FBI Issues Cybersecurity Threat Warning: American Oral Surgeons Urged to Increase Defenses The American Dental Association (ADA) and the American Association of Oral and Maxillofacial[...]

Why Car Dealerships Need To Invest In Cybersecurity
Why Car Dealerships Need To Invest In Cybersecurity: Immediate Action Required With an ever-increasing reliance on digital technologies, car dealerships are becoming prime targets for[...]

Prominent Cyber Threat Actors and Their Goals
Prominent Cyber Threat Actors and Their Goals The dynamic realm of cyber defense is perpetually challenged by sophisticated and well-organized cyber threat actors. These entities,[...]

What Are the Origins of Cyber Crime?
What Are the Origins of Cyber Crime: Tracing the Evolution of Digital Offenses Cybercrime, a phenomenon that has only emerged in the last few decades,[...]
Are You Just A Number To Your Current IT Services Company?
Experience Personalized IT Support: Tailored Solutions for Your Business Needs Businesses are challenged to obtain IT support that aligns with their specific needs. The surge[...]

Top Cybersecurity Tips for Your Employees
Top Cybersecurity Tips for Your Employees: Essential Strategies for Workplace Security In today’s digital age, protecting your organization’s data and systems from cyber threats is[...]
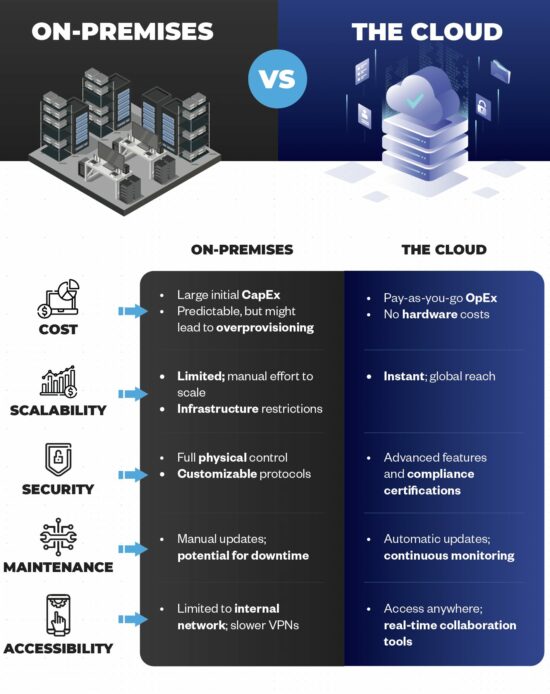
Comparing On-Premises Servers vs The Cloud
Comparing On-Premises Servers vs The Cloud: The Top 5 Differences Unveiled In today’s digital landscape, you are met with the pivotal decision of choosing between[...]

Top 10 Microsoft 365 Tips For Small Businesses
The Top 10 Microsoft 365 Tips For Small Businesses: Boost Efficiency and Productivity Microsoft 365 has become an indispensable tool for small businesses looking to[...]